- Home
- Who Uses Us
- Business SMS
- Cyber Attacks & Data Breaches

Cyber Attack and Data Breach Text Notifications
If you suspect that someone is trying to gain illicit access to online material, you need to send suspicious login alerts to the account holder as soon as possible. This allows you to stop the logins if the account holder is not responsible for them. This can be accomplished with mass SMS broadcasts.
Logging in to an online account is done by necessity. No one requires a login simply to access content that’s equal for everyone. Passwords are put in place to protect some sort of information.
And if whatever is being protected is important enough to require a password to access it, it’s important that a password alone isn’t the only thing keeping the information safe.
Why Send Suspicious Login Alerts via SMS?
If someone is trying to access content that they shouldn’t, it’s important to communicate the problem both immediately and clearly.
- Immediacy in response helps ensure that the problem doesn’t get more serious. Immediate notification means asking the true user if the incorrect password or strange location is really them. This allows everyone to know right from the beginning if there really is a problem at all. Text messaging is an ideal form of communication for suspicious login alerts because most people, especially in the professional world, keep their SMS-enabled devices near them at all times. Whether they’re in a meeting or sitting with their family at dinner, they will know immediately if their account is in danger.
- Clarity in response ensures that the recipient knows the severity of the situation but doesn’t blow it out of proportion. Clear communication allows the recipient to know precisely when and with what account the suspicious account activity occurred. When someone is stressed or panicked — as one may be when they think someone else is trying to gain access to their account — having all of the information in print in front of them, in a text message, can allow them to sort through for important information.
What Comes Next After Sending SMS Alert Notifications?
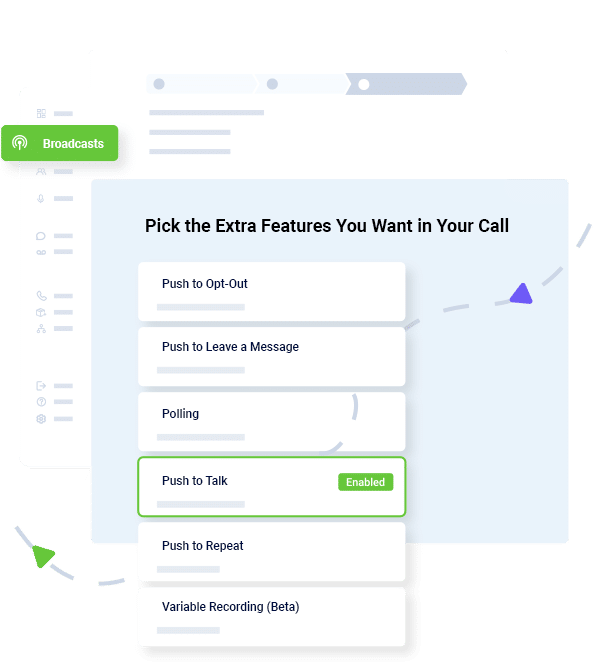
After a user has been notified of a suspicious login attempt, it’s important to hear back from them. If they’ve been alerted via SMS, they should be able to confirm or deny that it was truly them by replying to the message itself. In many cases, recipients can also call the number from which they received the message.
Whether texting or calling, the user can be navigated to speaking directly with a live representative, or led through a series of steps and questions to determine who can serve them best. This conversation can also lead them through troubleshooting steps that may help them identify what went wrong.
After the problem is identified and resolved, text messages can also be used to let the user know that the threat has passed. This can help restore a user’s faith in the system and build trust. The faster this notification happens, the faster the user stops worrying and the more at ease they feel in similar situations in the future, making the process ideal in business continuity plans.
- Home
- Who Uses Us
- Business SMS
- Cyber Attacks & Data Breaches
Try Using DialMyCalls Right Now
Start For Free
Send A Sample Broadcast
We'll send a sample call or text to your phone right now. Remember when you use DialMyCalls you can record your message in your own voice. When the phone rings just pick up and say "Hello" to hear the message.